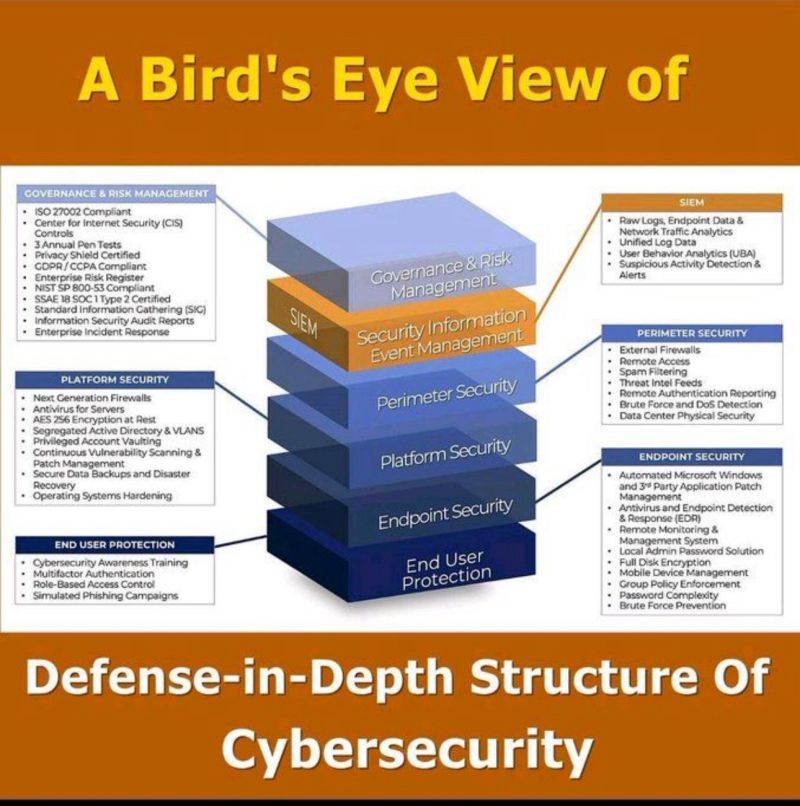
The chart here presents an illustrative guide to the multi-layered strategy known as “Defense-in-Depth” as a 3D pyramid with different levels, each representing a distinct layer of security measures and policies, underscoring the complexity and comprehensiveness required for effective cybersecurity defense.
At the top of the pyramid is “Governance & Risk Management,” which emphasizes the importance of compliance with standards such as ISO 27002 and the need for continuous monitoring and response to security incidents. This level sets the strategic framework for cybersecurity within an organization, including policy setting, risk assessment, and regulatory compliance.
The second level is “Security Information Event Management (SIEM),” which deals with the real-time monitoring, analysis, and reporting of security events and incidents. This layer is critical for identifying and responding to potential security breaches as quickly as possible.
Moving down the pyramid, “Perimeter Security” focuses on safeguarding the organization’s network boundaries from unauthorized access. This involves the use of firewalls, spam filtering, and intrusion detection systems to monitor and control incoming and outgoing network traffic.
“Platform Security” constitutes the next layer, with a focus on protecting the platforms on which applications and services run. This includes the deployment of next-generation firewalls, antivirus for servers, and secure configurations of operating systems.
The base level, “End User Protection,” highlights the importance of training end-users to recognize and avoid security threats, implementing robust access control measures, and conducting simulated phishing campaigns to prepare for potential attacks.
This multifaceted approach is required for robust cybersecurity, protection must be layered and integrated throughout all aspects of information technology. But there is no single solution to security; rather, an effective defense strategy requires a combination of tools, policies, and training.
ZEPSEC offers a complete platform for managing cyber threats from outside and inside your company. Get in touch to learn more about how we can improve your security posture within budget.